mirror of
https://github.com/dani-garcia/vaultwarden.git
synced 2026-04-06 04:42:00 +02:00
DNS lookup occurs before blacklist regex check #1913
Closed
opened 2026-04-06 02:39:30 +02:00 by MrUnknownDE
·
0 comments
No Branch/Tag Specified
main
cached-config-operations
test_dylint
1.35.4
1.35.3
1.35.2
1.35.1
1.35.0
1.34.3
1.34.2
1.34.1
1.34.0
1.33.2
1.33.1
1.33.0
1.32.7
1.32.6
1.32.5
1.32.4
1.32.3
1.32.2
1.32.1
1.32.0
1.31.0
1.30.5
1.30.4
1.30.3
1.30.2
1.30.1
1.30.0
1.29.2
1.29.1
1.29.0
1.28.1
1.28.0
1.27.0
1.26.0
1.25.2
1.25.1
1.25.0
1.24.0
1.23.1
1.23.0
1.22.2
1.22.1
1.22.0
1.21.0
1.20.0
1.19.0
1.18.0
1.17.0
1.16.3
1.16.2
1.16.1
1.16.0
1.15.1
1.15.0
1.14.2
1.14.1
1.14
1.13.1
1.13.0
1.12.0
1.11.0
1.10.0
1.9.1
1.9.0
1.8.0
1.7.0
1.6.1
1.6.0
1.5.0
1.4.0
1.3.0
1.2.0
1.1.0
1.0.0
0.13.0
0.12.0
0.11.0
0.10.0
0.9.0
Labels
Clear labels
SSO
SSO
SSO
SSO
SSO
SSO
SSO
SSO
SSO
SSO
SSO
SSO
SSO
SSO
SSO
SSO
SSO
SSO
Third party
Third party
Third party
Third party
Third party
Third party
Third party
Third party
Third party
Third party
Third party
Third party
Third party
Third party
Third party
Third party
Third party
Third party
Third party
Third party
Third party
Third party
Third party
Third party
Third party
Third party
Third party
Third party
Third party
Third party
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
better for forum
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
bug
dependencies
dependencies
dependencies
dependencies
dependencies
dependencies
dependencies
dependencies
dependencies
dependencies
dependencies
documentation
documentation
documentation
documentation
documentation
documentation
documentation
documentation
documentation
documentation
documentation
documentation
documentation
documentation
documentation
documentation
duplicate
duplicate
duplicate
duplicate
duplicate
duplicate
duplicate
duplicate
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
future Vault
future Vault
future Vault
future Vault
future Vault
future Vault
future Vault
future Vault
future Vault
future Vault
future Vault
future Vault
future Vault
future Vault
future Vault
future Vault
future Vault
good first issue
good first issue
good first issue
good first issue
good first issue
good first issue
good first issue
good first issue
good first issue
good first issue
good first issue
good first issue
good first issue
good first issue
good first issue
good first issue
good first issue
good first issue
good first issue
good first issue
good first issue
good first issue
good first issue
good first issue
good first issue
good first issue
good first issue
good first issue
good first issue
good first issue
good first issue
good first issue
hacktoberfest-accepted
hacktoberfest-accepted
help wanted
help wanted
help wanted
help wanted
help wanted
help wanted
help wanted
help wanted
help wanted
help wanted
help wanted
help wanted
help wanted
help wanted
help wanted
help wanted
help wanted
help wanted
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
low priority
notes
notes
notes
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
question
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
troubleshooting
wontfix
wontfix
wontfix
wontfix
wontfix
wontfix
wontfix
wontfix
wontfix
wontfix
wontfix
No Label
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
enhancement
Milestone
No items
No Milestone
Projects
Clear projects
No project
Assignees
 MrUnknownDE
MrUnknownDE
Clear assignees
No Assignees
Notifications
Due Date
No due date set.
Dependencies
No dependencies set.
Reference: github/vaultwarden#1913
Reference in New Issue
Block a user
Blocking a user prevents them from interacting with repositories, such as opening or commenting on pull requests or issues. Learn more about blocking a user.
Delete Branch "%!s()"
Deleting a branch is permanent. Although the deleted branch may continue to exist for a short time before it actually gets removed, it CANNOT be undone in most cases. Continue?
Originally created by @viglianesed on 11/10/2022
Subject of the issue
Vaultwarden server does a DNS lookup before checking the icon blacklist regex. https://github.com/dani-garcia/vaultwarden/blob/main/src/api/icons.rs#L264
This could cause deanonymization of the server owner/users.
Deployment environment
Install method: Docker
Clients used: n/a
Reverse proxy and version: n/a
MySQL/MariaDB or PostgreSQL version: n/a
Other relevant details: n/a
Steps to reproduce
A network DNS filtering solution like Pi-hole is recomended or any solution that logs DNS traffic.
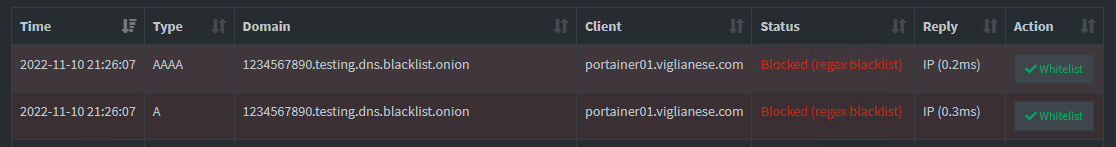
"icon_blacklist_regex": "'^(.*\\.onion/.*)$'",or in the admin page, setIcon blacklist Regexto'^(.*\.onion/.*)$'.onionurl like ->http://1234567890.testing.dns.blacklist.onion/Expected behaviour
For privacy reasons, the
lookup_host((domain, 0)).awaitshould happen after the regex check.Actual behaviour
The regex part works and it doesn't contact the actual server:
The issue is that some user's may not filter
.onionDNS requests, so the DNS requests will be sent to the upstream DNS server where they will be most likely logged and identify the user as a Tor user.Troubleshooting data
Screenshot of a blocked DNS query:
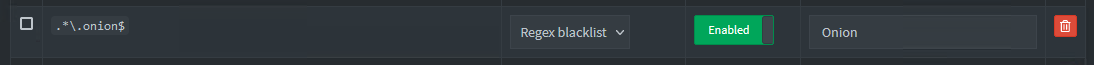
Screenshot of the DNS regex blacklist rule: