# 🧅 Tor Guard Relay
[](https://github.com/r3bo0tbx1/tor-guard-relay/actions/workflows/release.yml)
[](https://github.com/r3bo0tbx1/tor-guard-relay/releases/latest)

[](https://hub.docker.com/r/r3bo0tbx1/onion-relay)
[](LICENSE.txt)
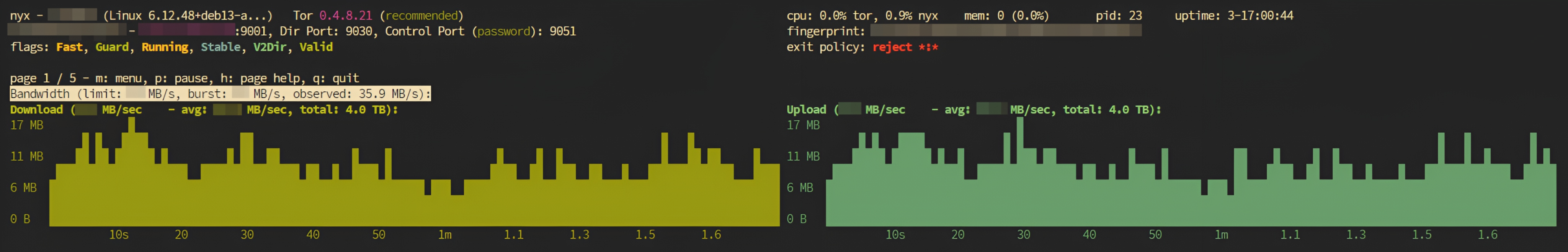
**A hardened, production-ready Tor relay with built-in diagnostics and monitoring**
[Quick Start](#-quick-start) • [Features](#-key-features) • [Documentation](#-documentation) • [FAQ](docs/FAQ.md) • [Architecture](docs/ARCHITECTURE.md) • [Tools](#-diagnostic-tools) • [Contributing](#-contributing)
 **A hardened, production-ready Tor relay with built-in diagnostics and monitoring**
[Quick Start](#-quick-start) • [Features](#-key-features) • [Documentation](#-documentation) • [FAQ](docs/FAQ.md) • [Architecture](docs/ARCHITECTURE.md) • [Tools](#-diagnostic-tools) • [Contributing](#-contributing)
**A hardened, production-ready Tor relay with built-in diagnostics and monitoring**
[Quick Start](#-quick-start) • [Features](#-key-features) • [Documentation](#-documentation) • [FAQ](docs/FAQ.md) • [Architecture](docs/ARCHITECTURE.md) • [Tools](#-diagnostic-tools) • [Contributing](#-contributing)